The email invitation asking you to sign in and RSVP to Donna Lopez’s Halloween party catches you by surprise. You don’t know a Donna Lopez, but you open the email anyway because a party sounds like fun. In a second, however, you learn it isn’t a real invitation, but rather a reminder from University IT (UIT) of how insidious phishing campaigns can be.

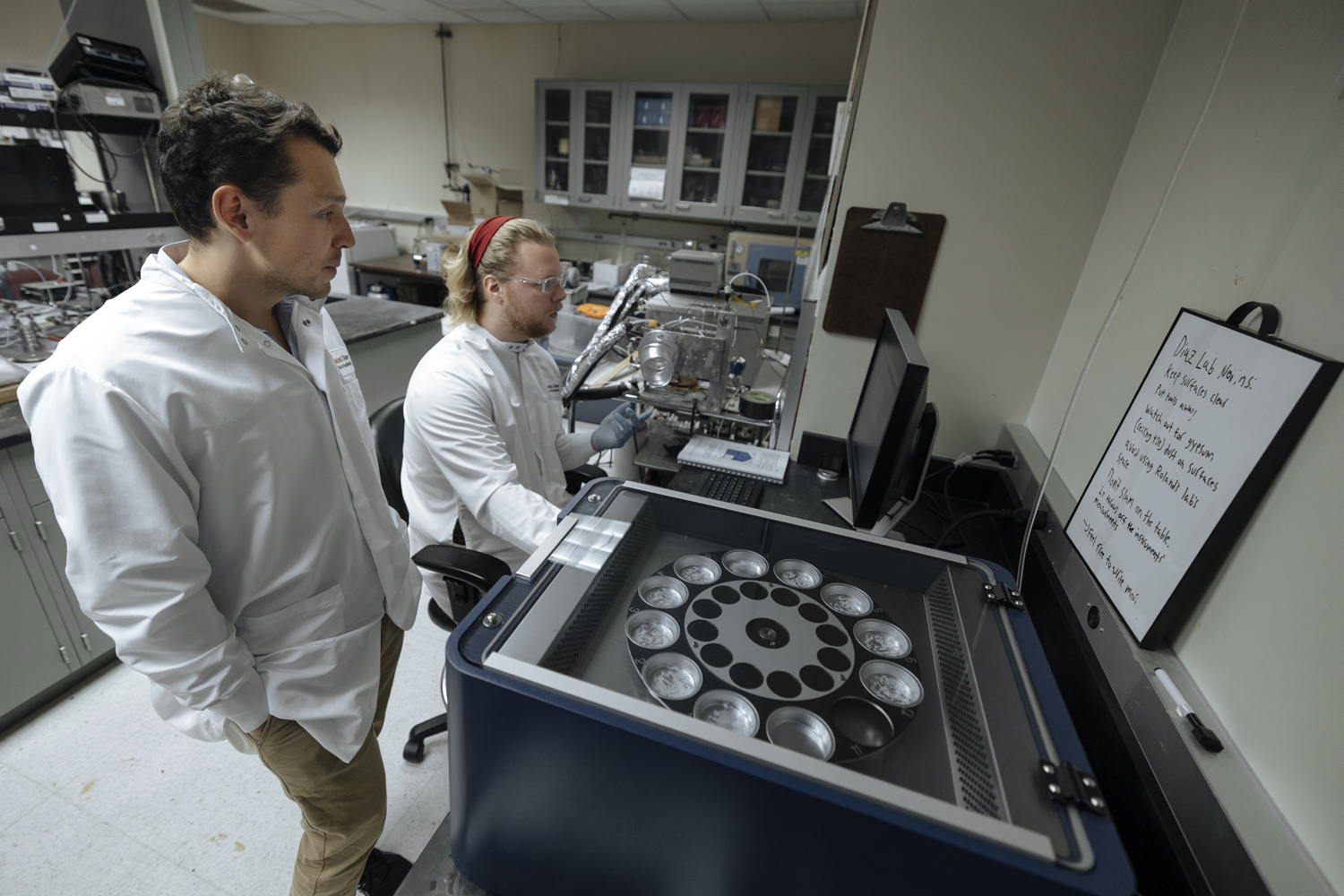
Michael Timineri, director of Information Security Consulting in the university’s Information Security Office, say phishing messages come to members of the Stanford community in many forms and commonly employ tactics that play on our sense of urgency, fear, curiosity, greed or desire to help. (Image credit: Stacy Lee)
The party invitation is part of Stanford’s Phishing Awareness Program, administered by the university’s Information Security Office (ISO) and expanded in May after a highly successful 18-month pilot project involving approximately 3,000 recipients. The program, which now includes about 17,000 faculty and staff, is designed to help members of the campus community learn to recognize and protect the university – and themselves – from malicious emails.
Each week, a message that simulates a real phishing scam is sent. The expectation is that members of the campus community will recognize these emails as phishing attempts, not click on the links contained in them and report them to ISO by forwarding them to spam@stanford.edu. Beginning this month, those who do not click will be rewarded by being omitted from the following week’s simulation.
Michael Timineri, director of Information Security Consulting in ISO, answers questions about the program and shares what UIT is discovering about Stanford’s susceptibility to phishing.
Why is phishing considered the single greatest threat to our privacy and cybersecurity?
Phishing is pervasive and plays a role in the vast majority of cybersecurity incidents. On a daily basis, my office is made aware of multiple community members whose credentials have been compromised through phishing. Phishing messages come to members of the Stanford community in many forms and commonly employ tactics that play on our sense of urgency, fear, curiosity, greed or desire to help. These messages may prompt someone to click on a link, open an attachment, or provide credentials and other sensitive information to an adversary unknowingly.
While Stanford has many information systems in place to prevent the majority of malicious emails from reaching community members, phishing messages can be highly customized, using information that is publicly available on the internet to target recipients. Falling prey to a phishing message could lead to significant personal or organizational financial loss. Unfortunately, our office is made aware of compromises that originate from phishing messages on a daily basis. From an adversary’s perspective, phishing attacks are trivial to launch and cost almost nothing, and yet are highly effective. It is for this reason that the best defense is to ensure that each person is aware of how to identify and respond to suspicious messages.
What has UIT learned about the phishing susceptibility of faculty and staff since widening the Phishing Awareness Program in May?
Since the program’s expansion, we’ve seen increased awareness of the threats associated with phishing messages and a dramatic expansion in engagement by the broader campus community. So, the program is working as intended.
How do you measure the success of this program?
Success is measured in click rates, meaning how frequently people click on links in simulated phishing emails, and reporting rates over time. In other words, we look at how often people report simulated or actual phishing emails to spam@stanford.edu and what trends look like over time. Lower click rates and greater reporting is what we would like to see.
Because click rates vary widely from campaign to campaign, we repeat similar campaigns four times per year in order to have a more direct comparison. For example, a prior phishing simulation, pretending to be a notification of a missed package delivery, was not clicked on by 70 percent of the recipients, but a more recent simulation was not clicked on by 90 percent. That’s a substantial improvement.
While our simulated phishing system does track individual clicks, we never report out at the individual level. This is a “no harm, no foul” educational program and is not intended to be punitive in any way. If someone does click on a link in a simulated phishing message, they will be directed to educational materials, and that is all.
How do you come up with the fake phishing messages?
Our simulated phishing messages are taken from actual phishing threats that we see coming into the university or that are reported by our community to spam@stanford.edu. We try to keep our simulations as similar to real phishing campaigns as possible.
For example, staff in one Stanford department recently fell victim to a phishing email that contained a malicious attachment. That week, our department re-created the look and feel of the malicious email to use as our simulation to the broader community. The hope is that the simulation helps prevent others from falling victim to a similar malicious email in the future.
Is there a particular type of phishing message that we are most susceptible to?
Anytime a phishing message contains information that the recipient is expecting, such as a package delivery notification or an invitation to a seasonal party like a Halloween get-together, the click rate is high.
Users also tend to be more susceptible to “spear phishing” messages that are highly tailored to them. In one recent real-world phish, a tailored message attempted to extort money from Stanford community members using a customized message that did not include any attachments or links. Through the phishing awareness program many community members knew to report the suspicious message to us by forwarding it to spam@stanford.edu.
What’s considered “out of bounds” for the program?
There are two important things that we never do in this program. First, we never send messages masquerading as a Stanford unit or department, such as sending an email purportedly from University HR about a change to your benefits. We do not want to create unnecessary burden for a Stanford unit or department, which may have to field questions about the simulation. While we don’t do this, real attackers often disguise themselves as Stanford organizations.
We also do not masquerade as real companies. For instance, instead of FedEx, our simulated phishing campaign might be called FidEx.
Do you have any advice for those of us who want to avoid being phishing victims?
From a prevention standpoint, be wary of unsolicited or unexpected emails, even if they appear to be from someone you know or pertain to a subject in which you are involved. If you are unsure whether you can trust an email, call the sender to confirm its authenticity before clicking any links or opening any attachments. We’ve posted more information on how to avoid phishing attacks at phishing.stanford.edu.
What changes are you planning with the program moving forward?
Currently we send phishing simulations on a weekly basis. However, starting this month, we will reduce the frequency for users who consistently recognize our simulations.
While no additional changes are currently planned, in an effort to keep our community secure, we will shape programs such as this in ways that are applicable as email-based threats evolve.
Author
Kate Junco and Kate Chesley